MIT researchers have devised a method that could allow states to prove they’re disposing of nuclear weapons without giving away any of their technical details — which are considered state secrets.
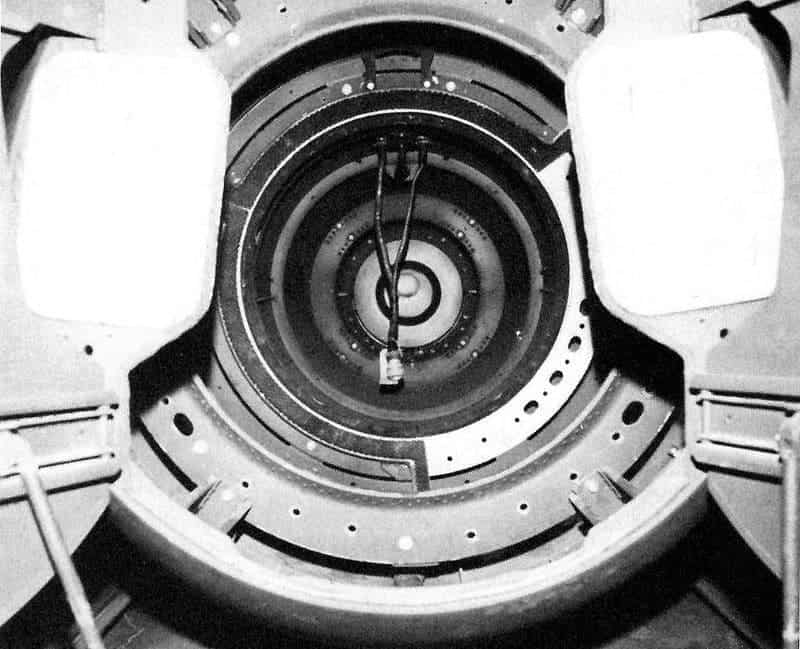
Image credits Scott Carson / US Atomic Energy Commission.
Nuclear disarmament negotiations (particularly those between the U.S. and Russia) always hit a patch of rough ground when verification processes come up. The main point of these talks is to promote nuclear non-proliferation — the understanding that the fewer nukes there are in the world at any one time, and the fewer actors there are with access to them, the easier it will be for humanity not to blast itself back to an irradiated stone age. However, every reliable verification process that the two parties could agree on as trustworthy (i.e. visually identifying the warheads) would give away technical data pertaining to the weapons.
This would never fly. For starters, governments don’t like other people to know how their nukes work — especially the people they’re generally aiming said nukes at. Secondly, such measures would risk disseminating technical details to third-parties, thereby defeating the whole purpose of disarmament efforts. Visual confirmation, then, became a no-go.
To spot a warhead
Now, an MIT research team reports developing a novel method of confirmation that could help promote nuclear disarmament without disseminating any state secrets. The method, similar to a physics-based version of cryptographic encryption systems, can be applied in two different versions — just in case one is found to have drawbacks by any government. The findings were published in two different papers.
Lacking a reliable tool to identify nuclear weapons, and thus bereft of a way to enforce their destruction, past agreements have focused on decommissioning of delivery systems. It makes sense, as it’s far harder to ‘fake’ a plane or a ballistic missile, whereas nuclear bombs are basically spheres of plutonium. Such measures have worked reasonably well up to now, but lead author Areg Danagoulian believes that it only skirted the real issue: to avoid such weapons falling into the hands of terrorist or rogue states, we need to dispose of the actual warheads — which means we need a reliable way to identify them or spot fakes, one to which governments will agree.
“How do you verify what’s in a black box without looking inside? People have tried many different concepts,” Danagoulian says. “But these efforts tend to suffer from the same problem: If they reveal enough information to be effective, they reveal too much to be politically acceptable.”
Their solution draws inspiration from digital data encryption methods, which alter data using a set of large numbers, which form the key. Without this key, the encrypted data is a hodge-podge of characters. However, while it may be illegible, it is still possible to tell if it is identical to another set of encrypted data — if they use the same key, the datasets would be the same hodge-podge. Danagoulian and his team applied the same principle for their warhead verification system — “not through computation but through physics,” he explains. “You can hack electronics, but you can’t hack physics.”
The method analyzes both of a warhead’s essential parts: the sphere of radioactive elements that supply its nuclear ‘gunpowder’, and the dimension of the hollow sphere called a pit that serves as a ‘detonator’ — details pertaining to both elements are considered state secrets. Because of this, they couldn’t simply probe the weapons’ internal characteristics, and they couldn’t tell a fake apart just by measuring emitted radiation.
Negative filter
So what the team did was to introduce a physical key, created from a mix of the same isotopes used in the weapon, but in a ratio unknown to the inspection crew. Similarly to a filter applied to a photo, the key will scramble information about the weapon itself. In keeping with that analogy, the physical key is like a complementary color filter (a picture’s negative) that will cancel out all of the weapon’s emissions when lined up properly. If the investigated object has a different emission pattern (i.e. it’s a fake), it will bleed through the filter, alerting the investigation crew.
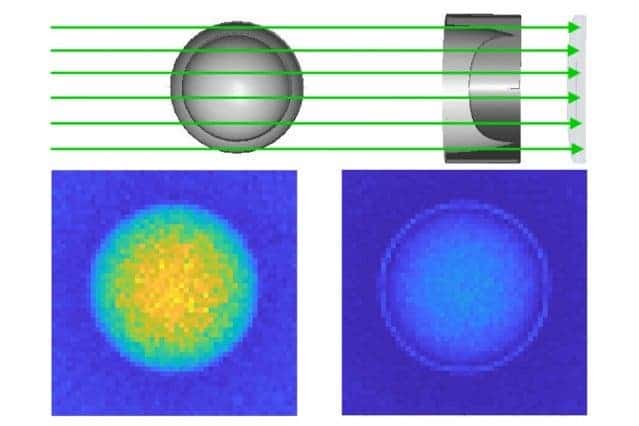
Image credits Areg Danagoulian.
This filter — called a cryptographic reciprocal or a cryptographic foil — will be produced by the same country that made the warheads, thereby keeping their secrets safe. The weapon can be hidden in a black box to prevent visual inspection, lined up with the foil, then get blasted with a beam of neutrons. A detector will then analyze the output and render it as a color image — if the warhead is genuine, the image will be blank. The second variant of this process substitutes a photon beam for the neutron one.
These tests are based on the requirements of a Zero Knowledge Proof — where the honest prover can demonstrate compliance, without revealing anything more. It also benefits from a built-in disincentive to lie. Because the template is the perfect complement of the weapon itself, when superimposed over a dummy it will actually reveal information about the warhead’s composition and configuration — the very things states don’t want others to know about.
It’s a neat concept; the only issue I have with it right now is that it only works if all parties involved are genuine, and do actually create the right reciprocals for their warheads. Still, if the system does someday get adopted and helps bring about significant reductions in the number of nuclear weapons in the world, Danagoulian says, “everyone will be better off.”
“There will be less of this waiting around, waiting to be stolen, accidentally dropped or smuggled somewhere. We hope this will make a dent in the problem.”
The papers “Experimental demonstration of an isotope-sensitive warhead verification technique using nuclear resonance fluorescence” has been published in the journal Proceedings of the National Academy of Sciences; “Nuclear disarmament verification via resonant phenomena” has been published in the journal Nature Communications.






