UK home secretary lashed out at encryption, saying that it’s not for “real people” and that only “terrorists” use it. This point of view is not only blatantly wrong, it’s also dangerous. Let’s see why.
The duct tape that holds the internet together
In recent years, technology has often developed faster than society can keep up. Using bank cards instead of cash must have seemed like an abomination a while ago (and probably still does to some people), but it’s become the norm in most of the world. Paying for things on the internet? Seemed scary at first, now everyone’s doing it. Using a smartphone instead of a bank card probably seems highly insecure to most people, but it’s very popular in China. Cryptocurrencies like Bitcoin were disregarded as a joke until recently, but such opinions have been proven wrong by the thousands who made fortunes by buying and selling them. More often than not, the technology is there, we’re not just ready to trust it yet.
There are several reasons why this happens, but chief among them is encryption. According to Ross Anderson, a cryptography expert at the University of Cambridge, encryption is “the duct-tape that holds the internet together” — and that’s a very elegant way of looking at things. We trust encryption so much that we share our most intimate thoughts to friends on Facebook or Whatsapp. Doctors can even discuss patient care on WhatsApp. We trust the internet with our data all the time, and we also trust it with our finance details. All that is done thanks to encryption, which has slowly become an important pillar in our society — a pillar that politicians now want to tackle with through sheer ignorance.
Politicians try science. It’s not very effective

In an article written in The Telegraph, British home secretary Amber Rudd has claimed that end-to-end encryption is useful only for terrorists, and is not for real people.
“Nearly every plot we uncover has a digital element to it,” Rudd writes. “Go online and you will find your own “do-it-yourself” jihad at the click of a mouse.”
She goes on to say that real people don’t need this kind of security and we should replace it with a half-encryption — kind of hidden, but allowing the government to peek in whenever it wants. Aside from being scarily Orwellian, this is also simply not possible and shows just how little the likes of Rudd understand of the process. Arguably, it’s a difficult concept to grasp, but this level of ignorance can hardly be justified.
Things can either be encrypted or not. Having a backdoor in encryption is basically having no encryption at all (if not worse). Rudd herself ponders this but slashes it with a nonsensical conclusion:
“That might be true in theory,” she writes. “But the reality is different.”
Yeah, that’s totally how things work. Sure, in politics you can lie your way to a new election, but you can’t lie your way to a new physical reality. Rudd does say that she doesn’t want to ban end-to-end encryption, but ends up asking for changes that amount to exactly that.
She isn’t isolated in this quest either. British Prime Minister Theresa May has requested the same thing and in a similar context, ad her Australian counterpart let out this gem:
“The laws of mathematics are very commendable but the only law that applies in Australia is the law of Australia.”
Rudd ends her article with a cherry on top, expressing her hope that the Silicon Valley geniuses can fix things. Seems like most interactions between politicians and scientists/engineers follow the same pattern: the former come up with impossible or severely flawed ideas, and the latter have to make things work. In the balance, this ends up affecting all of us, whether we realize it or not. We all cherish our privacy and security, or at least we should.
Paul Bernal, a senior lecturer at UEA Law School, told Business Insider via email:
“Amber Rudd’s comments are depressingly unsurprising — this is part of a bigger trend against encryption that we’ve been seeing for some time — and are based on a fundamental misunderstanding of both the technology and of privacy itself. From a technological perspective, it misses that creating an opening for law enforcement or the intelligence services creates an opening for all kinds of others — from criminals (and indeed terrorists themselves) to foreign powers, to malicious individuals.”
Why this can’t work
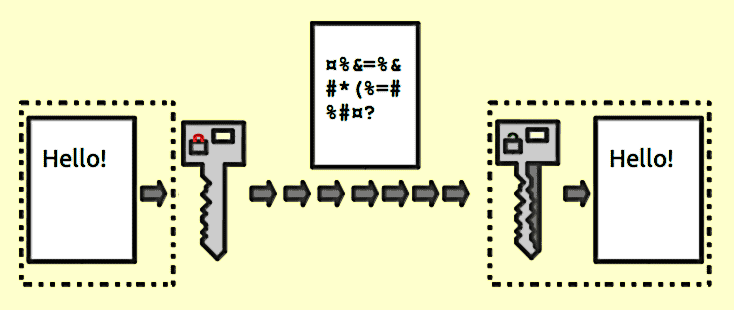
Companies such as Google, Facebook, and WhatsApp (now owned by Facebook) have been instrumental in developing end-to-end encryption. Basically, if you send a message to someone, it becomes almost impossible to crack without your approval. No one, not even the company can hack the message — only the sender and the recipient can access it.
This happens because alongside the message itself, the encryption algorithm generates ciphertext that can only be read if decrypted. It usually does this through a pseudo-random encryption key generated by an algorithm. The key to the decryption is only available to the sender and the receiver — so even if someone else were to intercept the message, they wouldn’t have the key to decrypt it. Basically, it would just be gibberish.
This is why what Rudd wants isn’t possible — because it just wouldn’t be encryption anymore. It’s pretty much all or nothing.
It is true that terrorists and other “baddies” take advantage of encrypted services. There’s no denying that. But to say that by forcing Facebook or Google to use half-baked security we would be fighting terrorism is wrong on many levels. For starters, many of those culpable for such atrocities were already known to intelligence staff. It’s not the mass surveillance that’s coming short, it’s the way that information is applied and enforced that needs improvement. Secondly, opening a back door into allegedly secure, private messages is just asking for trouble. MPs, business leaders, even home secretaries all use WhatsApp or similar software to communicate. If the message is accessible, it will be an invitation for hackers to see if they can breach it — and one thing we don’t have a shortage of is cyber attacks. Thirdly, who would guard the guardians? Namely, who will ensure that the government doesn’t illegally spy on its citizens? This is already happening in many parts of the world (yes, it’s probably happening to you too), do we really want to open another way of access for that?
But perhaps more importantly, you can never force all encryptors to leave the back door. As Facebook’s chief operating officer, Sheryl Sandberg, points out, we would just be pushing terrorists into darker corners, where we would know even less about them.
“If people move off those encrypted services to go to encrypted services in countries that won’t share the metadata, the government actually has less information, not more,” she said.
To make things even worse, there are open-access, free encryption services available online. What Rudd is asking for is the perfect way to make sure terrorists start using such alternatives, and this is where surveillance gets drastically harder.
This is also something that the people don’t want — not even those who voted to put Rudd and May into power. Mass surveillance is a fundamental threat to human rights, and while it’s more important than ever to tackle terrorism, it’s not here that more work needs to be done.
Still, Rudd says that “legislation is always an alternative.” It would be possible, in theory, for the UK to bring about the end of encryption. It wouldn’t even be surprising for a government led by the person who wrote a bill aptly nicknamed Snooper’s Charter, forcing Internet service providers and mobile phone companies to maintain records of each user’s internet browsing activity. After all, It would be yet another testament to how little politicians understand — or care about — the realities of a modern world. It also reads too much like a prequel to V for Vendetta to be comfortable with.