One of the most prolific smartphone viruses, which infected an estimated 10 million devices last year alone, is back with a vengeance. Known as HummingWhale, the malware is a new take on HummingBad — and it was embedded in some 20 different Android apps on the Play Store. The virus feeds ads to your devices to generate revenue for its makers.

For a society that spends much its time looking at screens, we’re laughably bad at keeping the bits of code behind them safe from tampering. Which is staggering, since we trust said code with our conversations, location, credit card information, and in some cases, pictures of our junk. A fact which certain groups are perfectly aware of and perfectly ok with cashing in on.
There’s no whale like a malwhale
Last year, cyber security firm Check Point stumbled upon HummingBad, a piece of malware that had infected more than 10 million Android devices through non-Google markets and shady sites — slowly minting money off of each one. It worked by silently downloading into Android devices running anything from Ice Cream Sandwich all the way up to Marshmallow, then attempting to wrestle root privileges through loopholes in the OS. If it failed to do this, HummingBad would prompt the user with a fake upgrade notification — during which it embedded itself in the OS.
For the most part, HumminBad was used to generate ad revenue by logging fake ad clicks from devices and performing unsolicited downloads to generate an estimated US$300,000 each month for Yingmob. It was one of the most advanced pieces of malware ever created and frustratingly difficult to remove. Eventually, though, Google shored up its software and security apps popped up all over to do just that.
But a new member of the family has been released upon the world, and experts are calling it HummingWhale. It infects devices by hitch-hiking on seemingly safe apps, 20 of which could be downloaded from the Play Store. Its end goal is largely the same as it’s predecessors — generate ad revenue for its programmers.
What it does
Check Point has been silently monitoring the Humming family for almost a year now, and reports that the new malware was downloaded between 2 and 12 million times already. They don’t believe Yingmob is behind Whale as well, but the two programs are obviously similar. The software is hidden in 5-star bot-reviewed apps uploaded by false Chinese companies. Its code is stored in a 1.3MB file called ‘assets/group.png‘ that matches many of the traits seen in HummingBad.
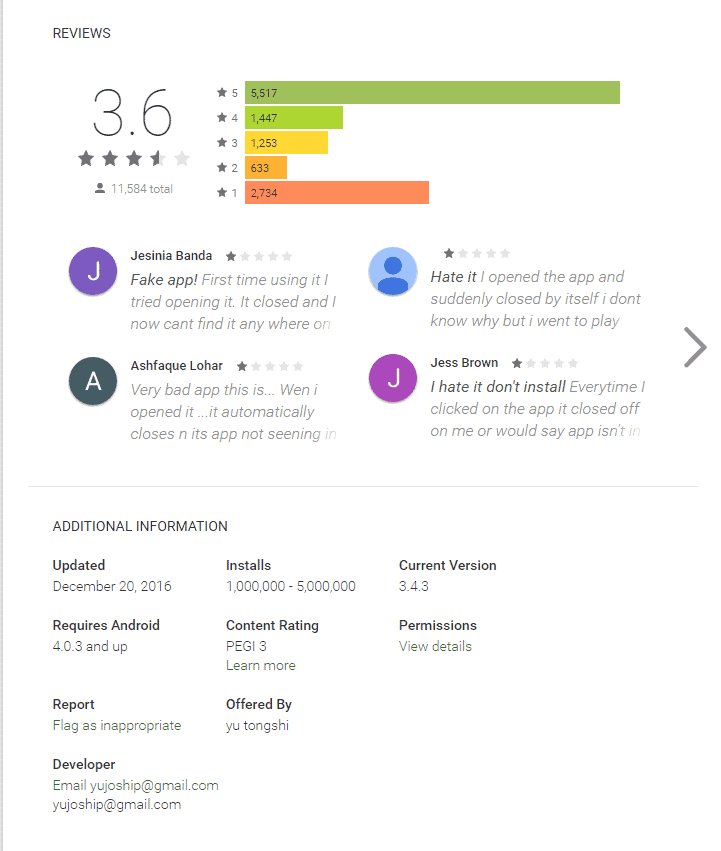
Image credits Oren Koriat / Check Point.
After download, the malware will display unsolicited ads that become increasingly harmful if opened. It doesn’t try to root devices any longer but creates a virtual machine on your device to perform ad fraud and automatically install apps, Check Point reports. It doesn’t require your approval to install these apps. It doesn’t need you to allow permission to use the device. And, if you close the ads or delete the apps, this functionality allows HummingWhale to continue running them in the virtual machine. It just stacks them up, as many as it likes.
“Once the user tries to close the ad, the app, which was already downloaded by the malware, is uploaded to the virtual machine and run as if it is a real device,” Check Point said. “This is a prime example of malware developers learning from each other, as tactics that were introduced by one of them are quickly adopted by others.”
“The fraudulent ratings left by such malware is another reminder that users cannot rely on Google Play for protection, and must apply further, more advanced means of security,” they urged.
Man the Harpoons
Because it can do stuff on your device without you having to approve or even know about, HummingWhale could become a security breach more glaring than the Death Star’s thermal exhaust.
Google has already removed the HummingWhale apps from the Play Store after Check Point alerted them. If you want to scan for the malware, Check Point has an app you can use. Lookout, one of Check Point’s competitors, also has an app set up as well — note that it treats the threat as part of the Shedun malware family.
Dan Gooding of ArsTechnica also recommends that the more tech-savvy among you can check if your device ‘connects to a control server located at app.blinkingcamera.com. Package names for infected apps typically contain a common naming structure that includes com.XXXXXXXXX.camera, for example com.bird.sky.whale.camera (app name: Whale Camera), com.color.rainbow.camera (Rainbow Camera), and com.fishing.when.orangecamera (Orange Camera)’. I’ve included a list of all known compromised apps and their naming structure below.
But if you suspect that you’ve got the Whale, it’s best to murder it violently with (digital) fire — back-up your data, write down your favorite apps, and perform a factory reset.
[panel style=”panel-danger” title=”Infected Apps:” footer=””] com.bird.sky.whalecamera – Whale Camera
com.op.blinkingcamera – Blinking Camera
com.fishing.when.orangecamera – Orange Camera
com.note.ocean.camera – Ocean camera
io.zhuozhuo.snail.android_snails -蜗牛手游加速器-专业的vpn,解决手游卡顿延迟问题
com.cm.hiporn – HiPorn
com.family.cleaner – Cleaner: Safe and Fast
com.wall.fast.cleaner – Fast Cleaner
com.blue.deep.cleaner – Deep Cleaner
com.color.rainbow.camera – Rainbow Camera
com.ogteam.love.flashlight – com.qti.atfwd.core
com.wall.good.clevercamera – Clever Camera
com.well.hot.cleaner – Hot Cleaner
com.op.smart.albums – SmartAlbums
com.tree.tiny.cleaner – Tiny Cleaner
com.speed.top – Topspeed Test2
com.fish.when.orangecamera – Orange Camera
com.flappy.game.cat – FlappyCat
com.just.parrot.album – com.qti.atfwd.core
com.ogteam.elephanta.album – Elephant Album
gorer – File Explorer
com.with.swan.camera – Swan Camera
com.touch.smile.camera – Smile Camera
com.air.cra.wars – com.qti.atfwd.core
com.room.wow.camera – Wow Camera-Beauty,Collage,Edit
com.start.super.speedtest – com.qti.atfwd.core
com.best.shell.camera – Shell Camera
com.ogteam.birds.album – com.qti.atfwd.core
com.tec.file.master – File Master
com.bird.sky.whale.camera – Whale Camera
cm.com.hipornv2 – HiPorn
com.wind.coco.camera – Coco Camera
global.fm.filesexplorer – file explorer
com.filter.sweet.camera – Sweet Camera
com.op.blinking.camera – Blinking Camera
com.mag.art.camera – Art camera
com.cool.ice.camera – Ice Camera
com.group.hotcamera – Hot Camera
com.more.light.vpn – Light VPN-Fast, Safe,Free
com.win.paper.gcamera – Beauty Camera
com.bunny.h5game.parkour – Easter Rush
com.fun.happy.camera- Happy Camera
com.like.coral.album – com.qti.atfwd.core
com.use.clever.camera – Clever Camera
com.wall.good.clever.camera – Clever Camera[/panel]
Was this helpful?