
No two fingerprints are the same, which is why a lot of people feel very confident that their high-end smartphones can’t be unlocked without their touch of approval. But that’s just wishful thinking since the technology manufacturers use creates vulnerabilities that a hacker can exploit in order to ‘guess’ the fingerprint similarly to PIN code brute force attack.
Meet the MasterPrint
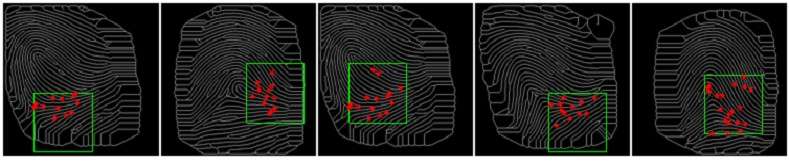
The fingerprint-based authentication systems you find in smartphones use very small sensors that only partially record and verify a person’s fingerprint. The smaller the area or resolution, the greater the likelihood that some of the patterns match features from another person’s fingerprint. Researchers at the New York University Tandon School of Engineering and Michigan State University College of Engineering claim these similarities could be enough for a hacker to create a ‘MasterPrint’ that has a chance to unlock devices given a large enough sample pool.
Nasir Memon is a professor of computer science at NYU Tandon and the study’s team lead. He says a MasterPrint is akin to the ‘1234’ PIN code password because both have a ‘4 percent’ match. Some 4 percent of PIN codes have the password ‘1234’ which is why hackers try this value first when attempting to guess the password. A MasterPrint matched at least 4 percent of other prints in a randomly selected batch.

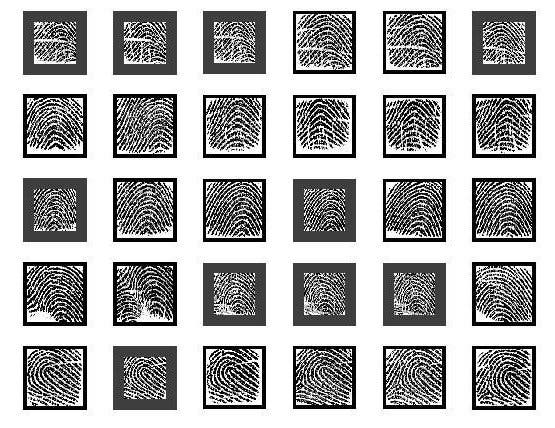
Memon and colleagues analyzed some 8,200 partial fingerprints with a commercially available fingerprint verification software and found 92 potential MasterPrints for every randomly selected sample bath of 800 partial prints. However, there was only one full-fingerprint MasterPrint in a sample of 800 prints, the researchers reported in IEEE Transactions on Information Forensics & Security.
“Not surprisingly, there’s a much greater chance of falsely matching a partial print than a full one, and most devices rely only on partials for identification,” said Memon.
After this first round, the researchers then designed an algorithm that can create synthetic partial MasterPrints. Remarkably, these had an even wider matching potential with experiments findings a successful matching between 26 and 65 percent of users. The matching varied wildly based on the number of partial fingerprint impressions stored for each use, all assuming a maximum of five authentication attempts. Specifically, the more partial fingerprints a smartphone stores, the more vulnerable it is to an attack.
Although the synthetic MasterPrints were simulated, the researchers emphasize that it’s not difficult for an attacker to transfer the print to physical artifacts to spoof a device. Moreover, the techniques involved in creating synthetic fingerprints can be refined for better results.
Manufacturers should take note, Memon and colleagues say, especially considering the fingerprint sensors are becoming increasingly smaller.
“If resolution is not improved, the distinctiveness of a user’s fingerprint will be inevitably compromised. The empirical analysis conducted in this research clearly substantiates this, said Michigan State University Professor of Computer Science and Engineering Arun Ross.
Previously, fingerprint authentification came under a lot of fire after the iPhone’s TouchID fingerprint authentication was hacked using lifted fingerprints. According to the study’s results, 40 to 50 percent of iPhone TouchIDs could be unlocked within the 5 tries if an attacker somehow wore a ‘glove’ with a MasterPrint on each finger. Apple, on the other hand, told the New York Times that “the chance of a false match in the iPhone’s fingerprint system was 1 in 50,000 with one fingerprint enrolled.” But since their fingerprint technology and records are secrets, there’s no way to verify this claim.
Besides adding a larger fingerprint sensor, the researchers recommend newer biometric security options, such as the iris scanner in Samsung’s new Galaxy S8. As for users, they recommend people disable fingerprint authentication for their most sensitive apps, such as mobile payments.
[interaction id=”58ef7f71cb4fa68908179ee9″]






