
The British Library has been attacked by cyber criminals on the 31st of October. This resulted in the library’s website going down and “some” data being leaked. Some of the library’s systems are paralyzed, some of its WiFi has been compromised, and the attackers now want to sell the leaked data to the highest bidder.
The great library heist
The British Library holds over 200 million items, including books, patents, and scholarly papers. The library also archives the UK’s web. Just last year, it collected 68 terabytes of web data. Everything is kept on a whopping 625 kilometers of shelves spread over 14 large floors — nine above ground and five below. The library is also an important attraction for tourists, locals, and scholars alike. Just a stone’s throw away from London’s central rail station, it draws over 11 million visitors every year.
But visitors to the British Library were greeted with an unusual message.
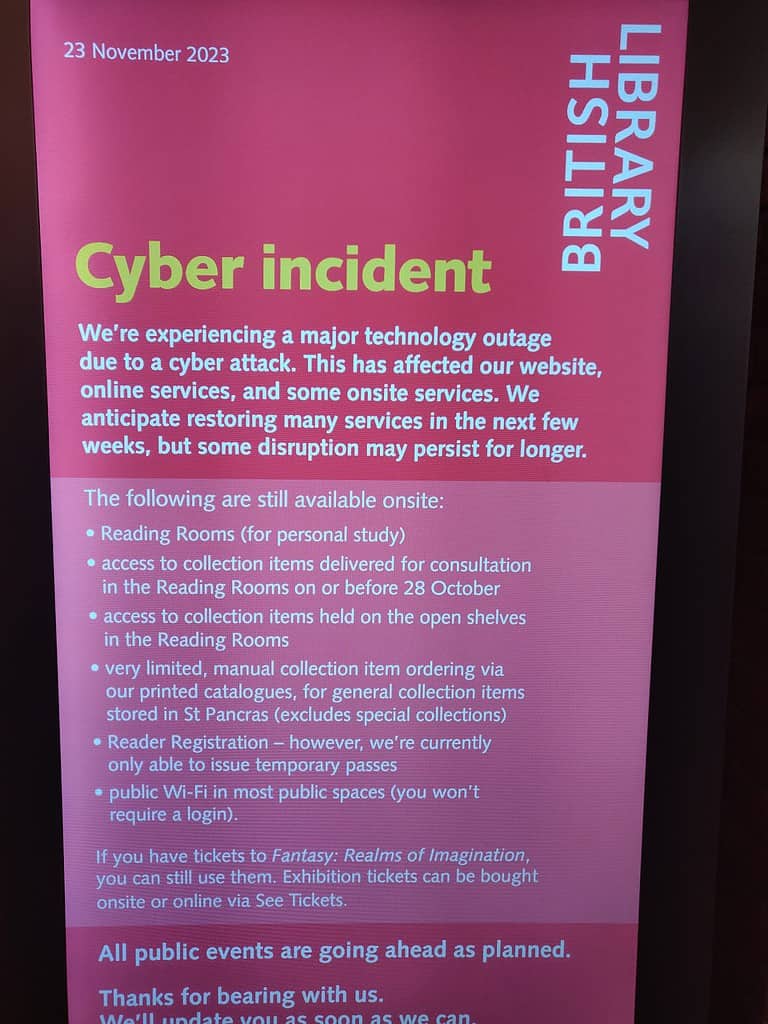
The British Library also posted a longer message on its Twitter page:
“We’re continuing to experience a major technology outage as a result of a cyber-attack. This is affecting our website, online systems and services, as well as some onsite services,” the announcement read.”
“Having confirmed that this was a ransomware attack, we’re aware that some data has been leaked. As a precaution, we recommend that if you have a password for British Library services that you use for other websites or services, that you change it on those accounts.”
Who did it?
The attack appears to be coordinated by Rhysida, a cyber-criminal group that originates in Russia. The group (named after a centipede) took responsibility for the attack and posted low-resolution photos of what appear to be contracts and passports of employees. ZME Science could not verify whether these were authentic. However, the British Library said it was “aware that some data has been leaked, which appears to be from files relating to our internal HR information”.
Rhysida said the data was “exclusive, unique and impressive” and they will sell it to a single buyer.
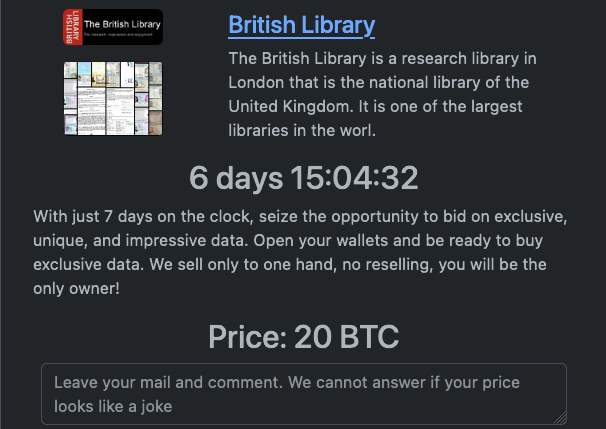
This extortion technique is not new. Rafe Pilling, a cybersecurity expert quoted by The Guardian, said that this is “a classic example of a double extortion ransomware attack.” Essentially, the attackers are using the threat of leaking or selling stolen data as leverage to extort a payment.
Just this year, Rhysida attacked cities in Portugal, the Chilean army, and the Kuwait Ministry of Finance using the same approach. British authorities are investigating the case but it is not clear whether the library is actually considering paying the ransom.
Rhysida may be new to the public, but authorities in the UK and other countries have been keeping an eye on the group since 2021. However, this year, the group appears to have ramped up its operations. Just two weeks ago, on November 15, the FBI and the US Cybersecurity & Infrastructure Security Agency issued a warning on the threat posed by Rhysida
“Threat actors leveraging Rhysida ransomware are known to impact ‘targets of opportunity’, including victims in the education, healthcare, manufacturing, information technology, and government sectors,” the statement read.
Cyber attacks are on the rise
Global cyberattacks increased by 38% in 2022, compared to 2021, and 2023 seems to keep a pretty similar trend. In fact, the global cyberattack number will likely continue to rise for the next few years. A third of all companies appear to have been targeted by such an attack.
There are many reasons why this happens. The proliferation of commercial cyber tools is on the rise. AI has turbo-fueled attacks, and even tools like ChatGPT can be useful for cybercriminals. Furthermore, many institutions and companies don’t protect their online data all that much, leaving an invitation for such an attack to happen.
To make matters even more shocking, ransomware attacks are sometimes successful. The average ransomware payments in the UK have nearly doubled to £1.2m over the past year. British authorities discourage against yielding to hacker demands, but paying the ransom is not strictly illegal. Given the high profile of the British Library, this could be an important precedent for future attacks.
The library estimates that over the next few weeks, most of its services will return to their normal state. What will happen to the leaked data (and if said stolen data is indeed authentic) remains unclear.






