The University of Melbourne recently co-organized a special a ‘cyber fox hunt’ event in which 12 teams were placed in the shoes of a data analyst working for the federal police. One of the teams, comprised of three pre-teens still in primary school, managed to track down a hypothetical whistleblower in under two hours. The team only metadata at their disposal; information like IP addresses, email addresses, phone numbers, and location data, which service providers are forced to store for two years by Australian law.
All but one team managed to track down the hypothetical ‘Minecorp’ employee who was emailing confidential information to an investigative journalist at ‘MineWatch’. The winning team took under an hour to find the whistleblower. This speaks about how easy it is to track a person — any person — using only abstract information.
Here’s what Gen, a 12-year-old from Team Sherlock, thought of it all.
“It was a lot easier than I expected,” she said.
“Basically what happened was we found the data that had the Google searches and the ones that corresponded with searches the whistleblower would use. We then found the IP address they used with the Google searches and we linked the IP address to their email. We used the email to find their phone number and their address.”
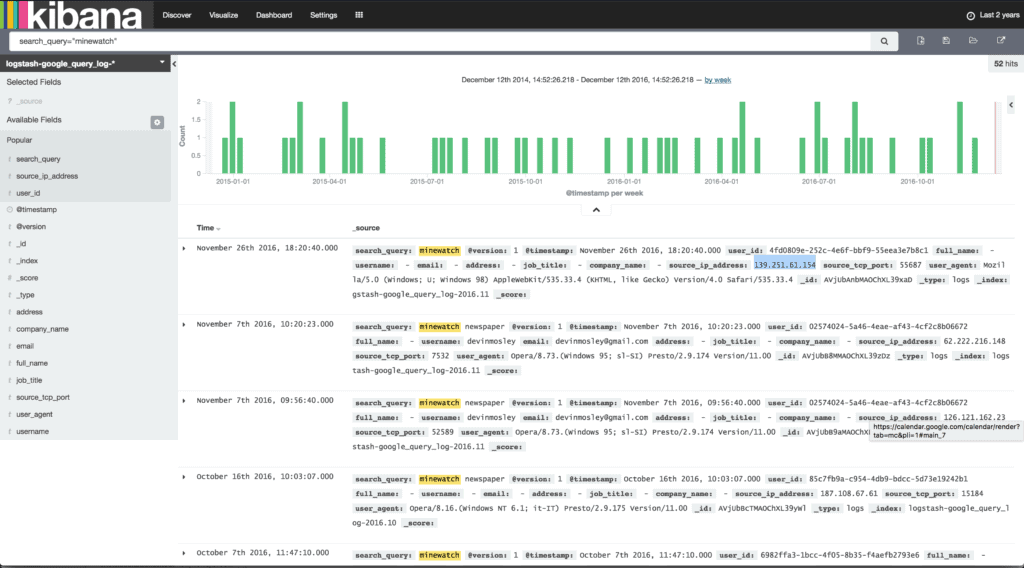
Using an analytics software called Kibana, the kids first mined the logs of Minecorp to see whether anyone had searched on Google for “MineWatch” or “Anna Dupont”, the name of the journalist who broke the story. They got a list of IPs who made the searches, which they then used as filters for e-mail addresses associated with these addresses. You can now search mobile providers databases to get the phone number and billing address linked to the e-mail.
Metadata stored by the Australian government also includes who emailed who and who phoned who. So, the kids only had to find out who e-mailed anna@minewatch.org.au. They could do this because they could also access Anna Dupont’s metadata.
Finally, the phone’s metadata also logs where a suspect whistleblower has traveled. Based on patterns, you can predict where the person will turn out and make an arrest.
Job done — and it took some 12-year-olds two hours to complete.
The purpose of this exercise was to show just how easy it is to use metadata, which you can theoretically use without a warrant in the land down under. Australia has been collecting metadata since October 2015, but the United States has been doing it for far longer, as a real whistleblower revealed. Elsewhere, metadata is used to track down and kill terrorists in drone attacks. The problem is the same metadata used to spot patterns sometimes fails and leads to innocent people ending up on the NSA’s kill list.
More than anything, though, this little experiment makes it very clear how metadata is a breach of privacy. The information that’s collected does not contain conversations or anything tangible, but even these ‘footprints’ are enough to track your activities — with ease.
Think you can do better than the pre-teens? Take the Snitch Hunt challenge and find out.
Was this helpful?