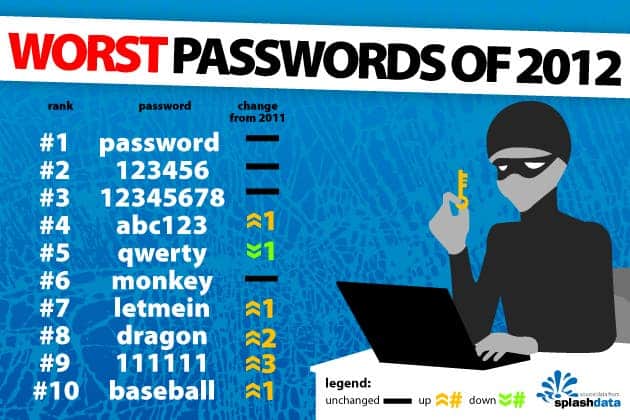
As computing power grows and becomes ever more accessible, passwords become easier to crack day by day. If you want to make it really easy for hackers and automated crawlers to retrieve your secure information then input passwords like common names, pets, sequences of numbers and symbols or birthdays. Yup, they’ll gobble these right up.
These are too easy though. For instance, Ashwini Rao and colleagues at the Carnegie Mellon University in Pittsburgh, Pennsylvania have developed a smart passsword cracking algorithm that not only looks for common password sequences, but also makes long keyword guesses that actually form a grammatically correct sentence. For instance some relatively advanced algorithms combine the same word in multiple varied instances, like “catscats” or the reversed “catsstac”. These algorithms however don’t know how to combine words to form sentences like “ilovebigcats”. Rao’s alogrithm, however, does.
The keywords are all retrieved from a password cracking database where common terms are listed. These are then combined by the algorithm in such an effective way that 10% of the total passwords cracked by Rao and her team were retrieved exclusively using their grammar-sensitive methods.
With this in mind, choosing grammatically incorrect passwords is a better bet. Also, in their research paper due for presentation at the upcoming Conference on Data and Application Security and Privacy in San Antonio, Texas, next month, the scientists warn that t other types of familiar structures like postal addresses, email addresses and URLs are very vulnerable passwords as well, despite being long or seemingly safe.
via New Scientist / image source
Was this helpful?